Du kan upprätthålla din integritet samtidigt som du säkerställer säkerheten för ditt onlinekonto genom att använda vår webbplatss tjänst Ta emot SMS. Vi erbjuder ett säkert och gratis sätt att få ett tillfälligt telefonnummer för SMS eller OTP-verifiering.
Varför används temporära nummer för SMS-verifiering?
Populariteten av SMS-verifiering har ökat, men det har också de svårigheter som har blivit följden av det.
Du måste ha tilltro till den andra parten för att ge dem din personliga kontaktinformation om du tillåter SMS-verifiering utan att använda en telefon.
Det finns många sätt på vilka detta kan exponera dig.
Riktiga SIM-nummer är en dyrare metod för att få ett tillfälligt telefonnummer än andra alternativ, men vissa använder dem för SMS-verifiering.
Jag tror det tar emot SMS har en mer kraftfull lösning på problemet.
Vad är motiveringen för företagens insisterande på SMS Online-verifiering?
Nuförtiden är många företag allvarligt oroade över intrång i informationssäkerheten.
Dataintrång kan nästan helt förstöra ett företags rykte, eftersom de är värdefulla.
Så istället för att ta chansen på cybersäkerhetsincidenter har majoriteten av organisationer lagt till SMS-verifiering som en extra säkerhetsåtgärd.
SMS-verifiering är verkligen inte hundra procent pålitlig.
SMS-verifiering är inte alltid pålitlig. Bara för att ett företag använder SMS-verifiering på något sätt betyder det inte att datasäkerhetsrisker elimineras.
Det ger dock företag ett legitimt argument i händelse av att kritisk data exponeras som ett resultat av ett dataintrång.
Är det möjligt att hoppa över SMS-verifiering?
Tyvärr kommer nästan alla enheter helt enkelt inte att tillåta dig att "välja bort" SMS-validering.
Spara gärna mitt mobilnummer i din adressbok så önskar jag dig lycka till.
Receive SMS can provide users with such a secure, short lived mobile number to replace your current phone number.
Please, try not to involve your telephone for SMS confirmation.
Organizations might be satisfied with SMS verification, however it doesn’t suggest that their shoppers are as satisfied.
Coming up next are instances of techniques through which people can do this:
- Buying a burner telephone or an expendable telephone
- Utilizing a contraption claimed by a companion or relative
- Looking on the Internet for “temp phone numbers for SMS verification“
- Utilizing Google Voice to speak with others
Potential Problems With SMS Verification in temporary numbers
Flera aspekter kan bara bli faktuella felaktiga när du använder en tjänst förutom att ta emot SMS för att verifiera SMS-meddelanden.
Ett exempel kan mycket väl vara:
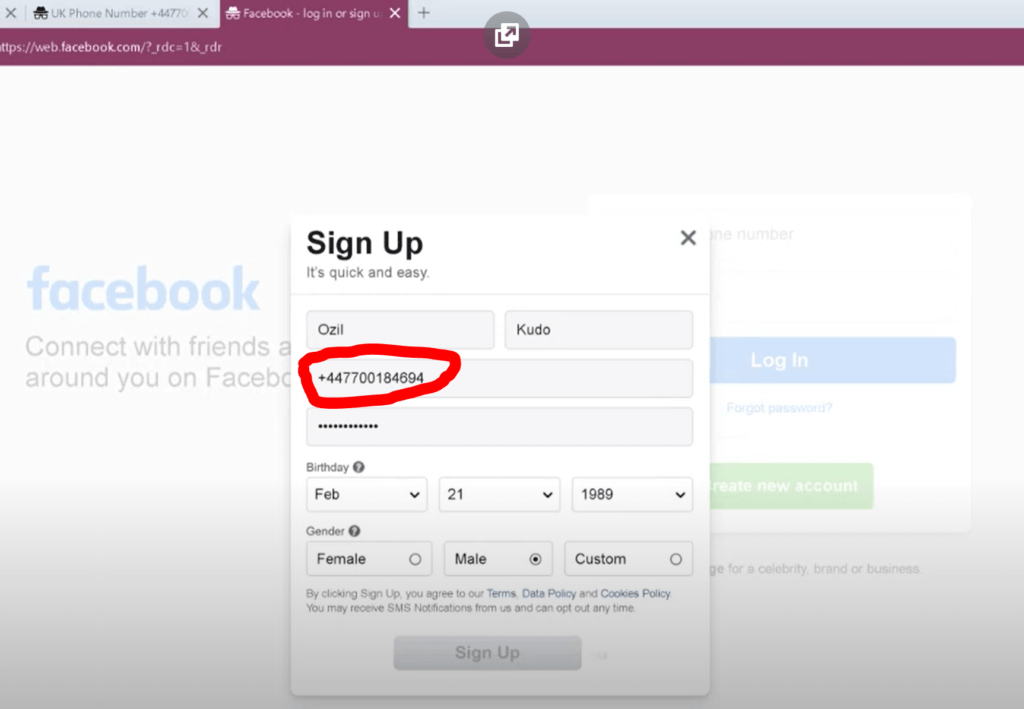
Användningen av webbplatser på internet tillhandahåller gratis tillfälliga telefonnummer är uttryckligen förbjudet på vissa sociala nätverkssajter, inklusive Facebook.
Du kanske inte får koden om du redan har aktiverat din telefons stör ej-funktion eller om du inte har en internetanslutning.
Vissa lösningar kanske inte skickar verifieringskoden när de garanterar.
Några av dessa applikationer för falska mobilnummer är osäkra, men andra kan samla in och sälja din personligt identifierbara information. Var försiktig när du använder dessa appar.
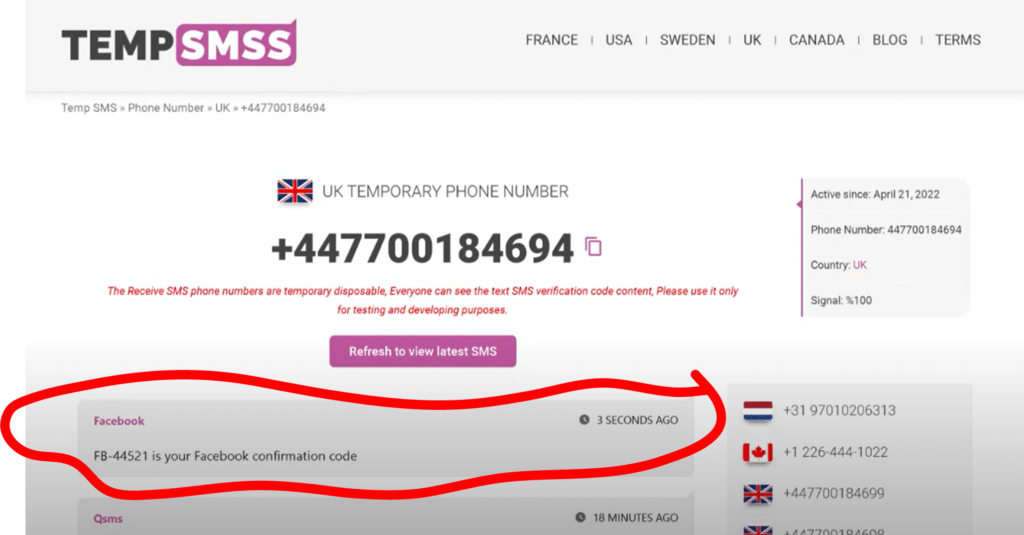
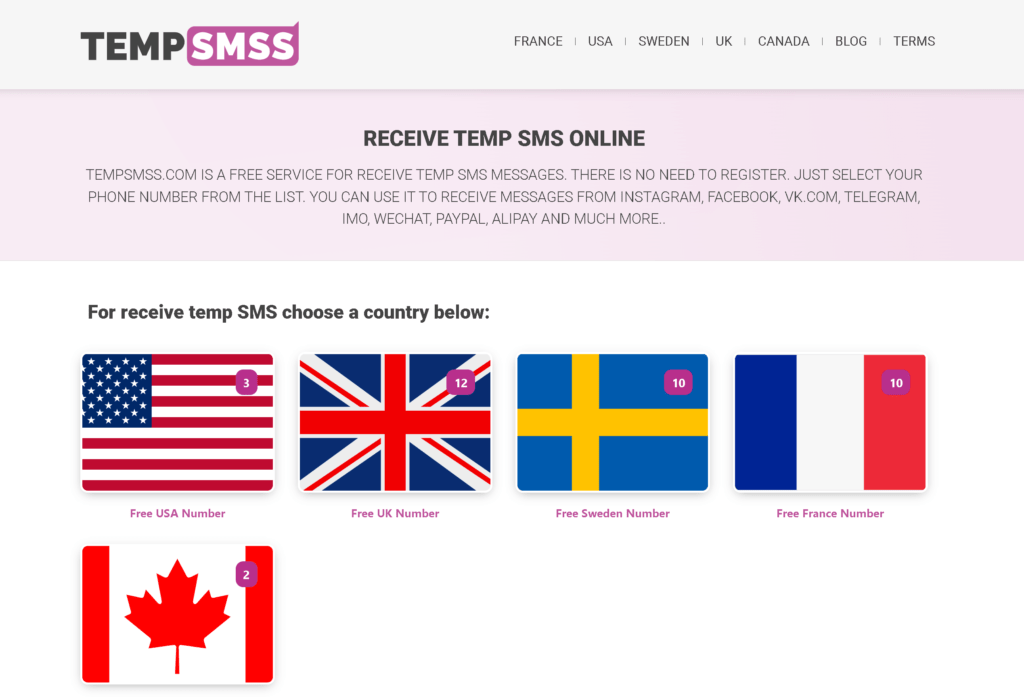
By using tempsmss.com, you’ll have the option to check SMS without having a telephone
With tempsmss.com, you’ll be able to get for digital services or indeed confirm SMS without the need for a mobile by using our temporary phone numbers opportunity.
The steps listed below should be followed:
- To get a new SMS receiver number, explore the main website then click on a country.
- Choose the number from a country you wish to get SMS from.
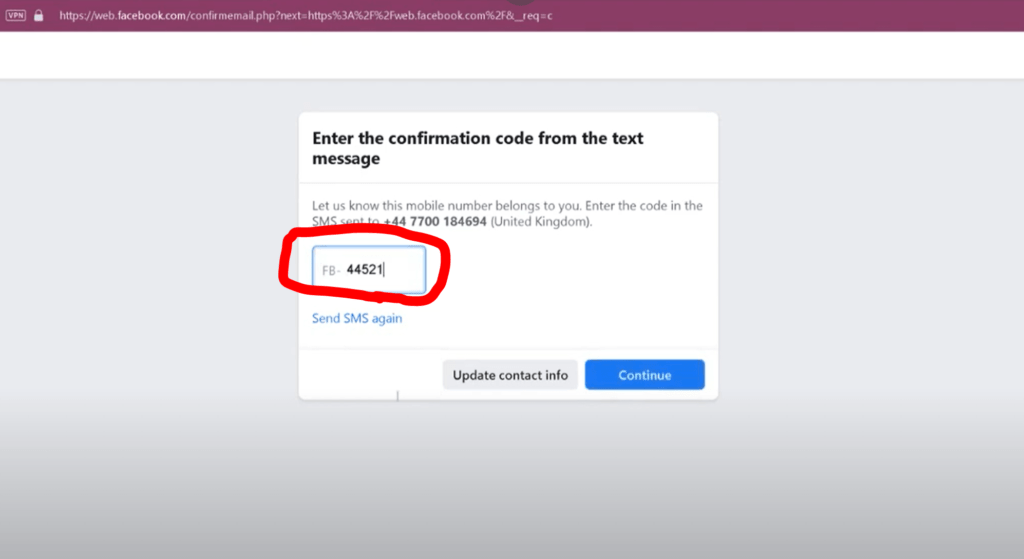
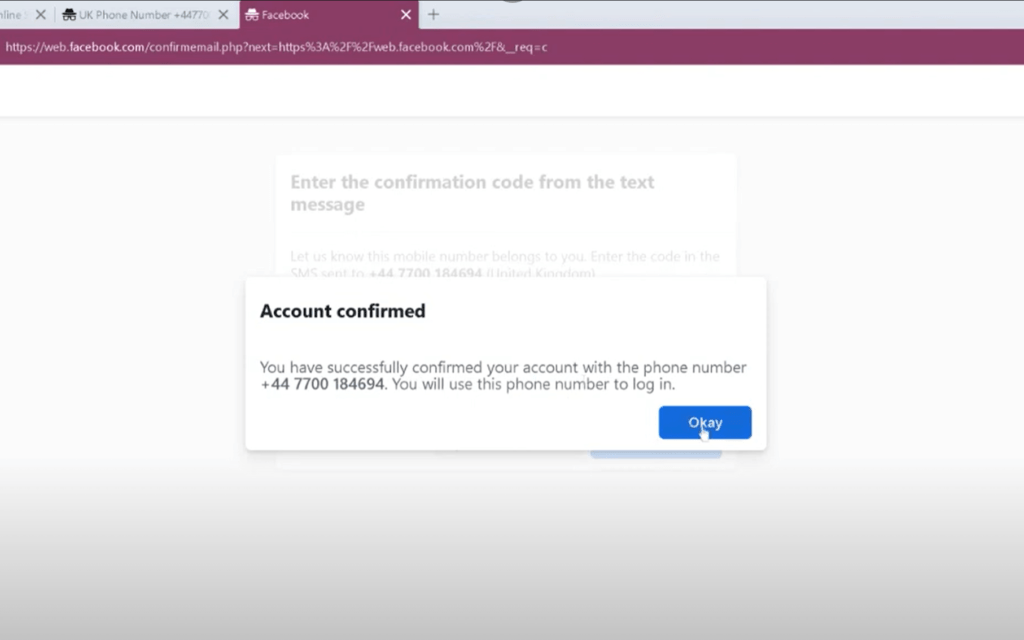
- As soon as you need to, start using your new temporary phone number. The attributed mobile number is abruptly cancelled and the text message is deleted after a minute.
- From the drop-down menu, choose “receive a temporary SMS” as a result, received SMS will show up in the page and it can only be used once before being tried to replace.
What else is available in tempsmss.com, besides this?
A suitable technique of information exchange is text messaging, especially for fast and easy messages or dialogues that don’t call for the use of a phone.
However when you want to text someone and you don’t have your phone with you, the issue emerges.
You might also not even have a phone contract or dislike using a smartphone’s keyboard because it is too tiny for you.
In any case, it might even be useful to know how to receive text messages on a laptop.
Fortunately, you have access to some tools that will help you with just this project.
Discover more by having read on.
There are several options for receiving messages out of your device, regardless of whether you don’t have a prepaid sim card or need to do so.
By choosing a few of the aforementioned options, you can receive texts quickly and easily without a phone.